|
% N; @1 `; \/ f6 @$ ?" w; T9 [
FTP (File Transfer Protocol) is a traditional and widely used standard tool for transferring files between a server and clients over a network, especially where no authentication is necessary (permits anonymous users to connect to a server). We must understand that FTP is unsecure by default, because it transmits user credentials and data without encryption. In this guide, we will describe the steps to install, configure and secure a FTP server (VSFTPD stands for “Very Secure FTP Daemon“) in CentOS/RHEL 7 and Fedora distributions. Note that all the commands in this guide will be run as root, in case you are not operating the server with the root account, use the sudo command to gain root privileges. Step 1: Installing FTP Server1. Installing vsftpd server is straight forward, just run the following command in the terminal. # yum install vsftpd2. After the installation completes, the service will be disabled at first, so we need to start it manually for the time being and enable it to start automatically from the next system boot as well: # systemctl start vsftpd# systemctl enable vsftpd ! M4 ?. ~0 l0 b/ r! c+ A
! N2 @9 T9 O$ [. k/ ]2 q, y3 Z
" t* p: d% g8 k% h$ ~- |5 c ! M4 ?. ~0 l0 b/ r! c+ A
! N2 @9 T9 O$ [. k/ ]2 q, y3 Z
" t* p: d% g8 k% h$ ~- |5 c3. Next, in order to allow access to FTP services from external systems, we have to open port 21, where the FTP daemons are listening as follows: # firewall-cmd --zone=public --permanent --add-port=21/tcp# firewall-cmd --zone=public --permanent --add-service=ftp# firewall-cmd --reloadStep 2: Configuring FTP Server4. Now we will move over to perform a few configurations to setup and secure our FTP server, let us start by making a backup of the original config file /etc/vsftpd/vsftpd.conf: # cp /etc/vsftpd/vsftpd.conf /etc/vsftpd/vsftpd.conf.origNext, open the config file above and set the following options with these corresponding values: anonymous_enable=NO # disable anonymous loginlocal_enable=YES # permit local loginswrite_enable=YES # enable FTP commands which change the filesystemlocal_umask=022 # value of umask for file creation for local usersdirmessage_enable=YES # enable showing of messages when users first enter a new directoryxferlog_enable=YES # a log file will be maintained detailing uploads and downloadsconnect_from_port_20=YES # use port 20 (ftp-data) on the server machine for PORT style connectionsxferlog_std_format=YES # keep standard log file formatlisten=NO # prevent vsftpd from running in standalone modelisten_ipv6=YES # vsftpd will listen on an IPv6 socket instead of an IPv4 onepam_service_name=vsftpd # name of the PAM service vsftpd will useuserlist_enable=YES # enable vsftpd to load a list of usernamestcp_wrappers=YES # turn on tcp wrappers5. Now configure FTP to allow/deny FTP access to users based on the user list file /etc/vsftpd.userlist. By default, users listed in userlist_file=/etc/vsftpd.userlist are denied login access with userlist_deny option set to YES, if userlist_enable=YES. However, userlist_deny=NO alters the setting, meaning that only users explicitly listed in userlist_file=/etc/vsftpd.userlist will be permitted to login. userlist_enable=YES # vsftpd will load a list of usernames, from the filename given by userlist_fileuserlist_file=/etc/vsftpd.userlist # stores usernames.userlist_deny=NO That’s not all, when users login to the FTP server, they are placed in a chroot’ed jail, this is the local root directory which will act as their home directory for the FTP session only. Next, we will look at two possible scenarios of how to chroot FTP users to Home directories (local root) directory for FTP users, as explained below. 6. Now add these two following options to restrict FTP users to their Home directories. chroot_local_user=YESallow_writeable_chroot=YESchroot_local_user=YES means local users will be placed in a chroot jail, their home directory after login by default settings. And also by default, vsftpd does not allow the chroot jail directory to be writable for security reasons, however, we can use the option allow_writeable_chroot=YES to override this setting. Save the file and close it. Securing FTP Server with SELinux7. Now, let’s set the SELinux boolean below to allow FTP to read files in a user’s home directory. Note that this was initially done using the the command: # setsebool -P ftp_home_dir onNow we will use semanage command to set SELinux rule to allow FTP to read/write user’s home directory. # semanage boolean -m ftpd_full_access --onAt this point, we have to restart vsftpd to effect all the changes we made so far above: # systemctl restart vsftpdStep 4: Testing FTP Server8. Now we will test FTP server by creating a FTP user with useradd command. # useradd -m -c “Ravi Saive, CEO” -s /bin/bash ravi# passwd raviAfterwards, we have to add the user ravi to the file /etc/vsftpd.userlist using the echo command as follows: # echo "ravi" | tee -a /etc/vsftpd.userlist# cat /etc/vsftpd.userlist9. Now it’s time to test if our settings above are working correctly. Let’s start by testing anonymous logins, we can see from the screen shot below that anonymous logins are not permitted: # ftp 192.168.56.10Connected to 192.168.56.10 (192.168.56.10).220 Welcome to TecMint.com FTP service.Name (192.168.56.10:root) : anonymous530 Permission denied.Login failed.ftp>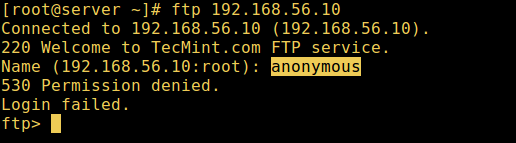 Test Anonymous FTP Login Test Anonymous FTP Login10. Let’s also test if a user not listed in the file /etc/vsftpd.userlist will be granted permission to login, which is not the case as in the screen shot below: # ftp 192.168.56.10Connected to 192.168.56.10 (192.168.56.10).220 Welcome to TecMint.com FTP service.Name (192.168.56.10:root) : aaronkilik530 Permission denied.Login failed.ftp>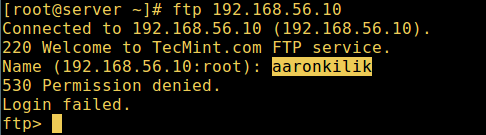 FTP User Login Failed FTP User Login Failed11. Now do a final check if a user listed in the file /etc/vsftpd.userlist, is actually placed in his/her home directory after login: # ftp 192.168.56.10Connected to 192.168.56.10 (192.168.56.10).220 Welcome to TecMint.com FTP service.Name (192.168.56.10:root) : ravi331 Please specify the password.Password:230 Login successful.Remote system type is UNIX.Using binary mode to transfer files.ftp> ls8 k Y* y5 F) ^4 N" y! n
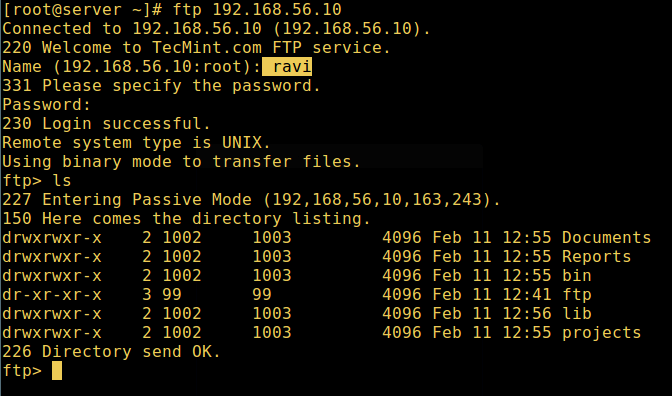 FTP User Login Successful[Warning: Using allow_writeable_chroot=YES has certain security implications, especially if the users have upload permission, or shell access. FTP User Login Successful[Warning: Using allow_writeable_chroot=YES has certain security implications, especially if the users have upload permission, or shell access.
0 z4 Q# b5 I7 D% u: A$ MOnly activate this option if you exactly know what you are doing. It’s important to note that these security implications arenot vsftpd specific, they apply to all FTP daemons which offer to put local users in chroot jails as well. Therefore, we will look at a more secure way of setting a different non-writable local root directory in the next section. Step 5: Configure Different FTP User Home Directories12. Open the vsftpd configuration file again and start by commenting the unsecure option below: #allow_writeable_chroot=YESThen create the alternative local root directory for the user (ravi, yours is probably different) and remove write permissions to all users to this directory: # mkdir /home/ravi/ftp# chown nobody:nobody /home/ravi/ftp# chmod a-w /home/ravi/ftp13. Next, create a directory under the local root where the user will store his/her files: # mkdir /home/ravi/ftp/files# chown ravi:ravi /home/ravi/ftp/files# chmod 0700 /home/ravi/ftp/files/Then add/modify the following options in the vsftpd config file with these values: user_sub_token=$USER # inserts the username in the local root directory local_root=/home/$USER/ftp # defines any users local root directorySave the file and close it. Once again, let’s restart the service with the new settings: # systemctl restart vsftpd14. Now do a final test again and see that the users local root directory is the FTP directory we created in his home directory. # ftp 192.168.56.10Connected to 192.168.56.10 (192.168.56.10).220 Welcome to TecMint.com FTP service.Name (192.168.56.10:root) : ravi331 Please specify the password.Password:230 Login successful.Remote system type is UNIX.Using binary mode to transfer files.ftp> ls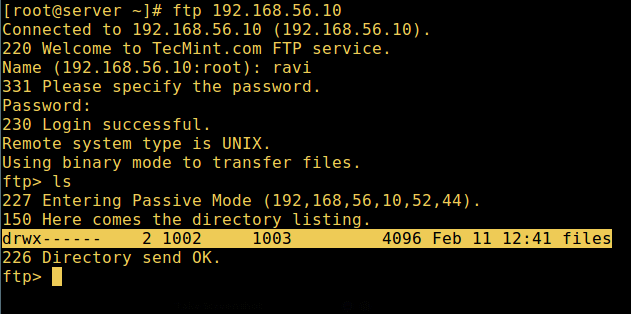 FTP User Home Directory Login Successful FTP User Home Directory Login SuccessfulThat’s it! In this article, we described how to install, configure as well as secure a FTP server in CentOS 7, use the comment section below to write back to us concerning this guide/share any useful information about this topic. |  |华强北 电脑城 龙岗电子世界 龙华电脑城 pc4g.com
( 粤ICP备16039863号 )
|华强北 电脑城 龙岗电子世界 龙华电脑城 pc4g.com
( 粤ICP备16039863号 )